Fixing TLS in Firefox
Warning: this post is now several years out of date. If you’re coming here from search results, please look elsewhere.
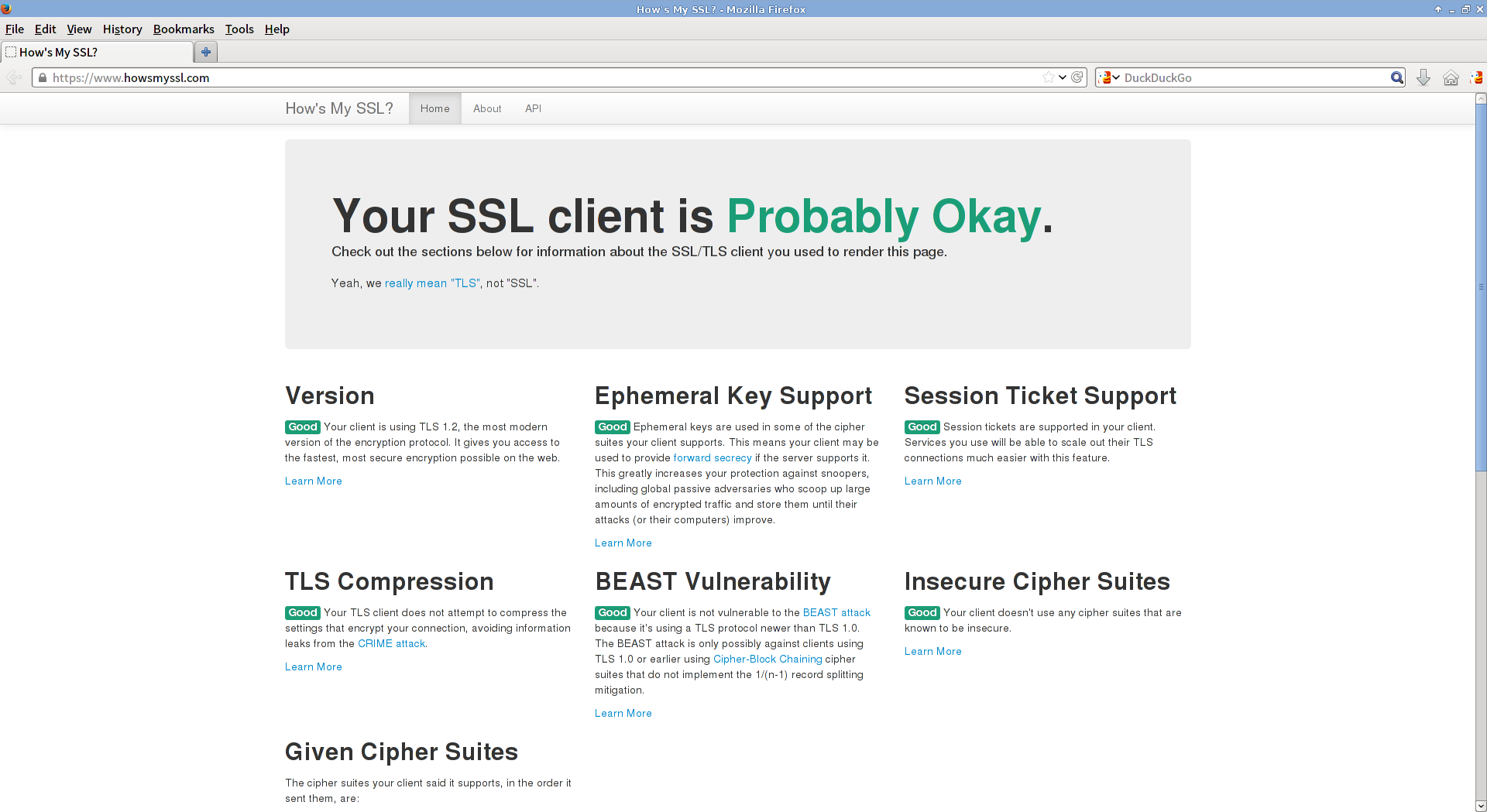
If you’re running a Firefox version between 19 and 26 (the latest at the time of
this post), you’re probably using insecure SSL/TLS settings despite the fact
that Firefox has support for TLS /1.[12]/. Luckily, it’s possible to quickly
fix this without sacrificing backwards compatibility. Simply visit
about:config and tweak the following settings:
security.ssl3.rsa_fips_des_ede3_sha false
security.tls.version.max 3
This enables up to date versions of TLS which aren’t vulnerable to the BEAST attack, and disables a known vulnerable SSL cipher that was discontinued with SSL3. If you’re using a FF version between 19 and 23, your max TLS version should be 2 instead since FF did not support TLS 1.2 at that time. This should make your connections more secure for servers that support TLS 1.1 and 1.2.
If backwards compatibility isn’t important to you, you might also set
security.tls.version.min to 2 and disable ciphers that use DES, RC2, RC4, or
MD5 (disabling RC4 will probably be the most drastic change as far as website
compatibility is concerned).
Warning: this is disabled by default because Firefox is vulnerable to downgrade attacks (see issue 861310). This should also work for Thunderbird and other Mozilla-based products. More (up to date) information can be found on Mozilla’s KB. Expect this to be the default setting in Firefox 27/Mozilla 28 (see issue 733647).
Update TLS 1.1 and 1.2 are now on by default in Firefox 27